How SOCLY.io simplifies your compliance
When Compliance Feels Like It’s Slowing Down Your Business
Build, Operate, and Certify Your ISMS With Confidence
We provide a structured, automation-first approach to ISO 27001 certification, helping modern SaaS teams replace manual coordination, fragmented documentation, and consultant-heavy processes with a single operational system.

Real-time monitoring












ISO/IEC 27001 is a globally recognized information security standard that establishes requirements for an Information Security Management System (ISMS). An ISO 27001 certification audit evaluates how organizations manage information security risks through structured risk assessment and Annex A controls. Certification by an accredited body validates the effectiveness of the organization’s information security governance and risk management framework.
ISO 27001 certification accelerates enterprise growth by establishing a globally recognized Information Security Management System (ISMS) aligned with ISO/IEC 27001 requirements. ISO 27001 certification strengthens vendor approval, speeds up procurement processes, and improves competitive positioning in regulated and international markets.ISO 27001 certification is a key trust indicator for scaling SaaS and technology businesses looking to expand their businesses across international borders.
Why is ISO 27001 Essential for Enterprise Tech?
ISO 27001 becomes critical when enterprise revenue depends on meeting international security standards and clearing global procurement reviews efficiently. Without certification, organizations may face slower deal velocity, extended procurement cycles, and limited access to regulated or cross-border opportunities.
Why is ISO 27001 Beneficial to the Health Tech Industry?
This practical guide explains what ISO 27001 certification involves,how the Information Security Management System (ISMS) works, the different stages in the ISO 27001 audit process, and factors that affect the ISO 27001 certification process in terms of time and costs. You’ll learn how to organize your risk assessment process, implement Annex A controls, build a stronger information security governance structure, and meet global procurement needs.
The goal is to reduce effort, not add complexity
No matter how ISO 27001 fits into the overall security strategy of your organisation, SOCLY.io manages execution for you, so your team can remain focused on growth.
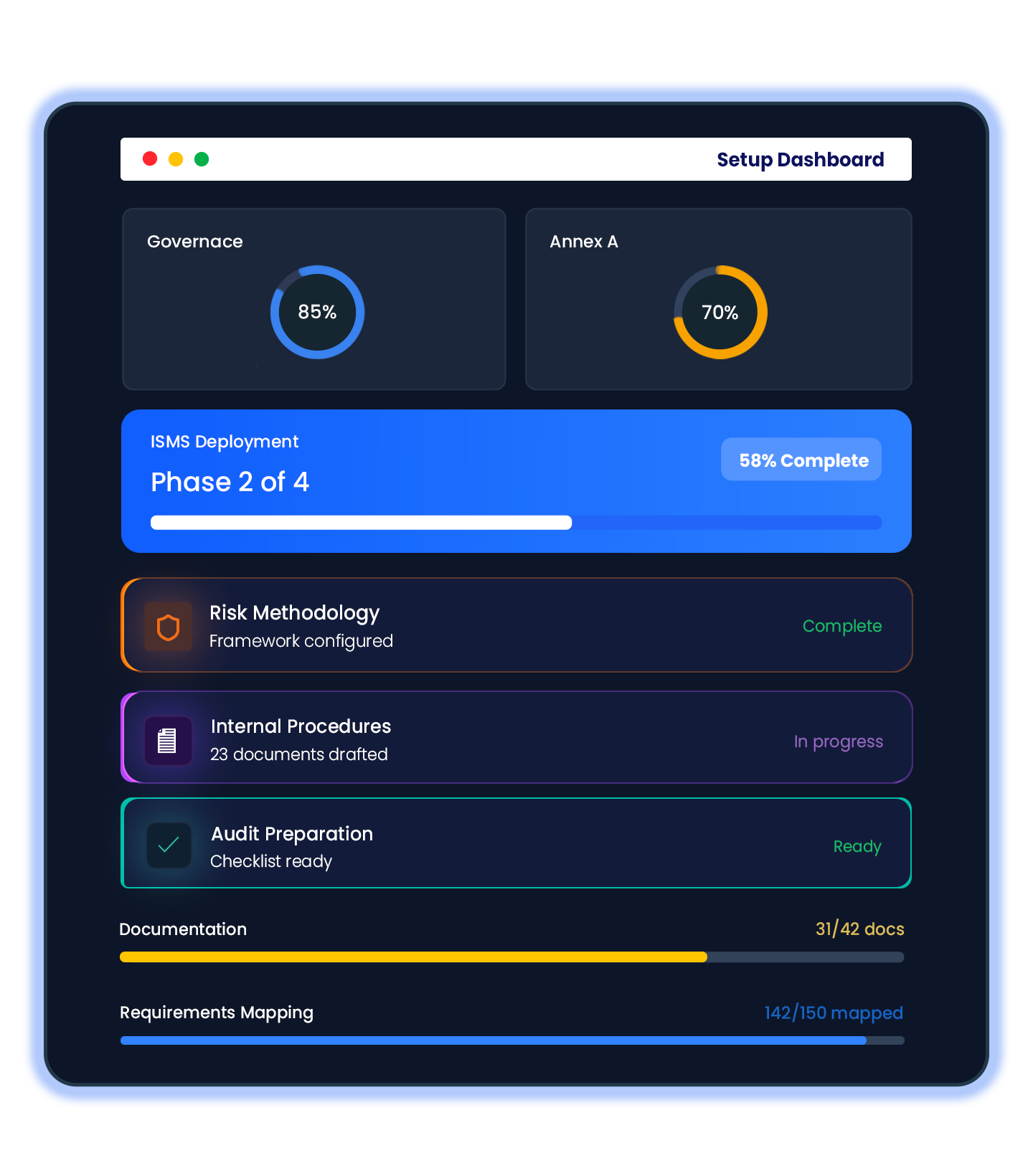
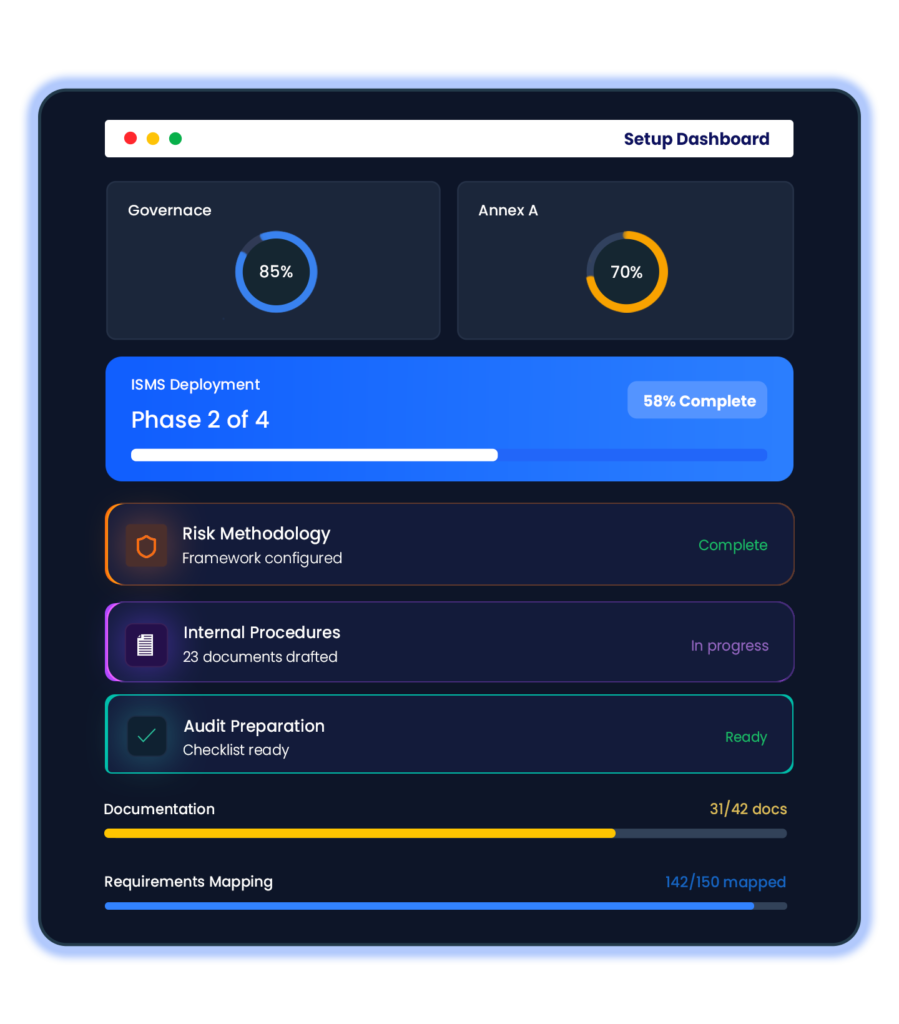
From scratch, we architect and deploy your ISO 27001 Information Security Management System. Business and technology requirements are mapped directly to governance, risk methodology, Annex A control implementation, internal procedures, documentation, and audit preparation.
You do not have to study ISO standards. To achieve certification, requirements are translated into clear, actionable steps.
We integrate with your infrastructure, access management, and engineering tools to continually demonstrate control effectiveness for ISO 27001 audits. Without manual tracking or document management, everything stays up to date.
No chasing of documents. No version confusion. No panic during audit
To ensure your organisation is ready for certification, our team assists with ISMS scoping, risk evaluation, control selection, gap remediation, and readiness checks. The audit process is structured, predictable, and minimally disruptive because we coordinate directly with certification bodies and auditors.
From scratch, we architect and deploy your ISO 27001 Information Security Management System. Business and technology requirements are mapped directly to governance, risk methodology, Annex A control implementation, internal procedures, documentation, and audit preparation.
You do not have to study ISO standards. To achieve certification, requirements are translated into clear, actionable steps.
We integrate with your infrastructure, access management, and engineering tools to continually demonstrate control effectiveness for ISO 27001 audits. Without manual tracking or document management, everything stays up to date.
No chasing of documents. No version confusion. No panic during audit

To ensure your organisation is ready for certification, our team assists with ISMS scoping, risk evaluation, control selection, gap remediation, and readiness checks.
The audit process is structured, predictable, and minimally disruptive because we coordinate directly with certification bodies and auditors.

A single system manages every core component of an ISMS governance, risk management, security controls, workforce processes, and quality management.
Configure ISO 27001 documentation according to your organization’s scope, operating model, and risk posture, without starting from scratch.

To maintain ISO 27001 compliance, employee onboarding, access validation, security awareness training, and device posture checks are continually mapped to ISO 27001 control objectives.
Continual risk evaluation and control verification help keep your ISMS remain effective between audits, not just during certification audits.
Ensures customers and partners are aware of ISO 27001 controls, certification progress, and security posture through a centralized Trust Center.
A centralized vendor assessment, monitoring, and incident tracking service that’s aligned directly with ISO 27001 supplier relationship controls.
Stay aligned with ISO 27001 throughout implementation and beyond certification with continuous monitoring and periodic reviews. Identify gaps early, keep controls updated, and maintain a consistent audit-ready posture
ISO 27001 should not be the end of your information security program it should be the foundation. Reuse your established Information Security Management System (ISMS), documented risk assessment processes, and Annex A controls to expand into additional regulatory and assurance frameworks without rebuilding your security program from scratch.
Our platform correlates and maps your ISO/IEC 27001 control environment to other globally recognized standards, enabling identification of overlapping controls and closing existing gaps to expedite multiple framework certifications.
Adapt your SOC 2 control environment to safeguard Protected Health Information (PHI) and meet healthcare security requirements.
Translate your ISO 27001 control framework into SOC 2 readiness by mapping ISMS controls to the Trust Services Criteria, supporting enterprise security reviews and vendor assurance requirements.
Leverage your existing information security controls and risk management framework to strengthen personal data protection and align with GDPR obligations across EU markets.
When Compliance Feels Like It’s Slowing Down Your Business
Building a startup isn’t easy; in fact, it is always a learning process for everyone, whether the startup is being…
Healthcare companies handle some of the most valuable information in the world, such as pharmaceutical R&D information and the most…
Let us help you achieve SOC 2 compliance efficiently and effectively
ISO 27001 is a globally recognized international standard for information security. This framework helps the organizations to protect the data of their customer and business through a structured Information Security Management System (ISMS).
The framework majorly focuses on identifying the risks by applying security controls and continuously improving the security practices. However, ISO 27001 is a certification that is issued after an audit done by an accredited certification body.
The ISO 27001 certification is essential for some businesses, because:
ISO 27001 certification generally has two main stages:
The ISO 27001 certificate is valid for 3 years, with the annual surveillance audits.
ISO 27001 is especially important for organizations that handle sensitive customer and business data, including:
The timeline for obtaining ISO 27001 certification depends on several factors, however, the estimated time is as follows:
But, if you have the right tools and guidance in place then the certification can be achieved faster.
The cost of getting ISO 27001 certification done varies based on several factors, including:
However, the typical costs included in the process are as follows:
There are no hidden costs, however, if there are any hidden costs then it generally comes from manual processes and poor planning.
Yes, startups also need ISO 27001, especially the B2B and global-focused startups. The ISO 27001 certification helps startups in many things, including:

Establish responsible AI governance with structured AI risk management, transparency controls and global compliance readiness.

Implement an Information Security Management System (ISMS) to manage information security risks and meet international enterprise expectations.
Protect EU personal data and align with European data protection regulations, cross-border data transfer requirements, and privacy governance standards.
Secure Protected Health Information (PHI) and meet U.S. healthcare data security and privacy requirements.
Comply with California Consumer Privacy Act requirements and strengthen consumer data protection transparency.
Align with India’s Digital Personal Data Protection Act to manage personal data processing obligations and regulatory compliance.
Your trusted partner in compliance automation. Turn complex regulations into clear, automated workflows.
By submitting, you agree to our Privacy Policy and Terms of Service